Pictures and videos from eyewitnesses at the scene of a news event are now central to how such events are reported, but news organisations are still tripped up by fake or old footage. From the recent Brussels attacks to those in Paris and Lahore, the verification of imagery has sometimes come second place to being first to publish.
During part of the recent FDLive training at The New York Times, Eyewitness Media Hub director Claire Wardle detailed five steps in the verification process: understanding the provenance of a picture or video and whether it is original; verifying the source; verifying the date it was captured; verifying where it was captured; and understanding the motivation of the eyewitness in taking it.
The steps are laid out in the First Draft Verification Guide in more detail, and Wardle suggested a range of tools and techniques for journalists to work through the stages.
“None of them are perfect on their own,” she said, “but if you put them all together it gives you a pretty strong foundation to do your work.”
Provenance
Reverse image search
“The most simple but most important” way to find the origin of a picture online is through a reverse image search, said Wardle.
Tools like Google’s image search or TinEye allow users to scour databases for matches of an image, to see if it has appeared online before.
For Google Chrome users, the plugin RevEye is especially effective as it will automatically run an image through both Google and TinEye, as well as Bing, Russian web service Yandex and the Chinese Baidu.
However, if reverse image searches returns no matches, “that doesn’t mean ‘amazing, we can use it’,” she said. it means we have to carry on doing more checks.”
YouTube Data Viewer
A similar service for videos is still not available however, but there are some workarounds.
Amnesty’s YouTube Data Viewer can help by providing frames from a video with which to carry out a reverse image search.
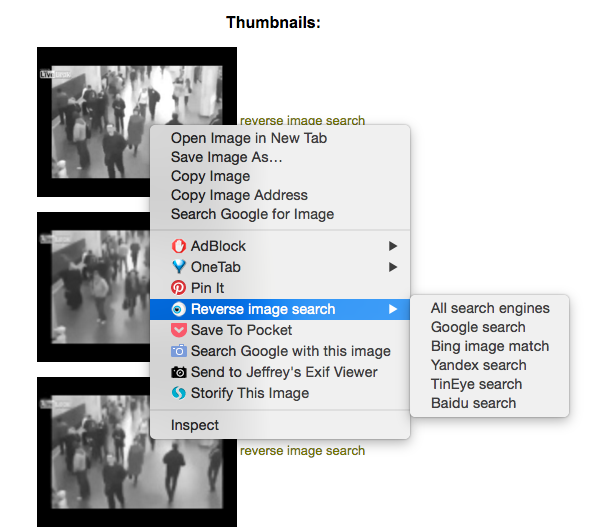
This video of the subway bombing in Minsk in 2011 was recirculated during the Brussels attacks. Thumbnails provided by YouTube Data Viewer can be searched for with RevEye when using Google Chrome
“Although we haven’t found the answer for reverse video search, this is the closest we can get,” said Wardle.
Izitru
The ultimate aim should be to speak to the source of the photo though, she said, and ask them to send the original image file.
“Without that it’s very difficult to know if you are looking at the original.”
If a source does email what they say is an original image, Wardle recommended the free tool Izitru to check whether an image has been altered before sending it. The results aren’t always conclusive, but if Izitru does not mark an image as green – for ‘high trust’ – it is not likely to be a camera-original image.
Source
PeekYou, Pipl and Spokeo
With the amount of personal information people now make public on the internet and the interconnectivity of various social networks and services, tracing someone’s digital history and identity is easier than ever.
PeekYou, Pipl and Spokeo all tap into these networks of identifying information, although they generally reap more results for people in the US, Wardle said.
Pipl is better for investigating sources outside the US, however, “but it’s only as good as the information people have put out there”.
“You always want a unique identifier,” Wardle added. “So rather than somebody’s name, you’re better to search someone’s email address or telephone number or username.
“The more unique your information is the better your results are.”
Foller.me
Another useful tool, especially for Twitter accounts, is Foller.me, which will give detailed information about a Twitter account – like account history and when tweets are published – which are useful in understanding whether an account is a bot, a spammer or a real person.
Graph.tips
One “freakishly upsetting” tool for investigating sources through their Facebook accounts is graph.tips, which allows users to see photos a person is tagged in, photos they have commented on, locations they have visited and more.
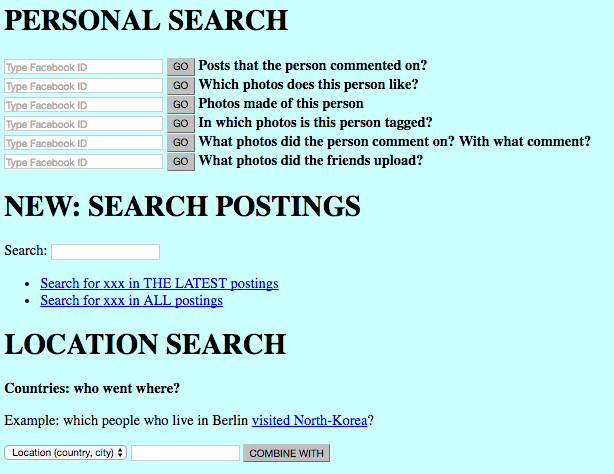
Screenshot from graph.tips
It only reveals public posts and comments, but can provide more information than a standard Facebook search.
Who.Is searches
If a user has a website associated with one of their social profiles, a Who.Is search will reveal the information they submitted when registering their domain name such as email or phone number.
Most people will pay extra to hide their identity from Who.Is searches, as Wardle has, but a smart trick to get around this is to look for similar domain names which may have been registered by the same person.
“Often people like me will buy clairewardle.com but might also buy clairewardle.co.uk and clairewardle.net or clairewardle.biz,” she said. “I’m not going to pay the extra $20 for [security on] the other domains because there’s nothing on them, but you could potentially go in and find my secret information.”
Date
Understanding time codes
Journalists need to understand how different social networks record the date of posts as a starting point to verifying the date of a picture or video.
In 2013, RT questioned the legitimacy of videos uploaded to YouTube alleging to show the Ghouta chemical weapons attack, claiming they were upoaded hours before the attack took place.
All YouTube videos are registered to Pacific time, 10 hours behind Syria, so when the first bombs fell at 02:30 on the morning of August 21, YouTube registered the videos which eyewitnesses filmed and uploaded as August 20. Rather than recorded before the events, they were simply uploaded from a later timezone.
Instagram dates posts to Pacific time, whereas Twitter shows the time and date relevant to the time zone a user viewing a post has selected in their settings, and Facebook displays the time and date a post was uploaded according to the timezone selected on a viewing user’s device.

Wolfram Alpha
As a “computational knowledge engine”, Wolfram Alpha is most useful in verification to research the weather of a particular location on a particular date.
It goes as far as showing cloud cover by hour and incidences of rain or other precipitation, which should be evident in photos of images taken outside.
Exif data
Every digital camera now embeds extra information in an image file, as well as the image itself: the date of capture, camera type, shutter speed and exposure, GPS data and more are all included.
Journalists can upload image files to Jeffrey’s Exif Viewer, said Wardle, to see all of this data and better understand the legitimacy of an image.
“Knowing what type of camera [an image] was taken on becomes important when talking to the source,” she said, as journalists can double check whether the camera they claim to have used matches the image’s metadata.
Location
Social media geotags
Twitter, Instagram and Facebook all now allow users to tag their location when posting to their network which, in theory at least, should help journalists verify where it is from.
This can be easily manipulated though. The below image was uploaded to Twitter in September 2015 and geotagged as Yemen during a period of vicious fighting in the country’s ongoing civil war. But the image itself is actually of the infamous ‘Highway of Death’, from the 1991 Gulf War.
والله لاهواستحقاربس ماكان داعي يدخلوبلادنا.
والله لاماحميناابلادنالاندي البنادق لنساء #اليمن_مقبره_الغزاه
ابوالحارث pic.twitter.com/KJlh7MDmDe— علي الشوذبي (@7728b9d554fd482) September 6, 2015
“The tweet is geolocated, but the content isn’t,” said Wardle, stressing that journalists need to be particularly careful with Facebook and Instagram as it is possible to override location tags.
Exif data
Another good reason to get the original file and look at the exif data, Jeffrey’s Exif Viewer will show not only where an image was captured but which direction the photographer was facing, making it easier to verify.

Jeffrey’s Exif Viewer will pin point the location an image was captured using its exif data, and even show the direction the camera was facing
Visual clues
“For most pictures or videos there are enough clues, even though it doesn’t look like it, to be able to independently geolocate where something was,” said Wardle, ideally by “putting yourself where the uploader was standing”.
In the Instagram image below, geotagged to the Idomeni refugee camp on the border with Greece and Macedonia, a number of clues stand out to help with geolocation.
A photo posted by Petar Panjkota (@panjac) on
The split in the train tracks, the pylons, the overhead wires, the small earth bank on the left and the foliage in the background are all clues to identify where the photo was taken.
The camp is easily identifiable on Google Maps by the tents and buildings close to the border which have sprung up in the last 18 months. Google’s Streetview function also reveals an image which very closely matches the features in the Instagram photo.

Screenshot from Google Maps of the Idomeni refugee camp on the border with Greece and Macedonia

Screenshot from Google Streetview which corroborates the Instagram image
Motivation
“We often forget who’s actually holding the camera,” said Wardle. “The way that we think about sources [as journalists], we forget about it when we talk about eyewitnesses.”
Eyewitnesses are a big part of the story rather than simply the uploader of a photo and can play a big role in telling the story better. Speaking to an eyewitness directly about their experience will inform the story, but can also go a long way in debunking their claim if they are trying to trick a news organisation.
Download the First Draft Verification Guide to print out and keep.



