This is the second in a series of new Essential Guides published by First Draft. Covering newsgathering, verification, responsible reporting, online safety, digital ads and more, each book is intended as a starting point for exploring the challenges of digital journalism in the modern age. They are also supporting materials for our new CrossCheck initiative, fostering collaboration between journalists around the world.
This extract is from First Draft’s ‘Essential Guide to Verifying Online Information’, by research reporter Shaydanay Urbani.
Download the full guide:
Verification of online content can be intimidating, but it is not difficult.
Being good at verification is mostly about repetition, persistence and using digital investigative tools with a little creativity. There are so many verification tricks and tools available now. In fact, the hardest part might be remembering all of the resources at your disposal.
That’s where this book comes in. This is your little condensed guide to the wizardry of verification. It includes essential concepts, checklists and our favourite tips and techniques. Most importantly, it will introduce you to the five pillars of verification, and hopefully serve as a quick reference for how to tackle each one.
Information travels so quickly now, and disinformation is becoming so easy to generate and spread that it is important for every journalist — not just the tech reporter and the social media editor — to understand basic verification skills.
This is especially true in a breaking news environment, when the pressure is high to both report quickly and get the facts straight. Newsrooms also need to protect themselves from being hoaxed and inadvertently introducing falsehoods to a wider audience. Many agents of disinformation see coverage by established news outlets as the end-goal and will use online spaces to seed rumours and manipulated content, hoping to reach a bigger audience.
For more information on this see First Draft‘s Essential Guide to Responsible Reporting in an Age of Information Disorder.
Verification is constantly changing. Tech platforms modify their privacy settings, research tools get taken down and new ones are built
Before verifying anything online, ask yourself this first most basic question: Is the content I am looking at connected to an event that actually took place?
In some circumstances, like a breaking news event, this question might be the very thing you are trying to ascertain with your verification. But in some cases it isn’t.
Imagine you find a video that claims to be of long lines and unhappy passengers at the Chicago O’Hare International Airport. Before you go down the rabbit hole of verifying the person who captured the video, the date and time, or the location, your first question should be this one: are there actually reports of problems at the airport?
Another example is the infamous headline that emerged ahead of the 2016 US election: Pope Endorses Donald Trump. You can do all the verification you like about the website, who created it, when the article was published and how far it spread, etc. but the fundamental claim of the article should be the first thing you check.
The 5 pillars of verification
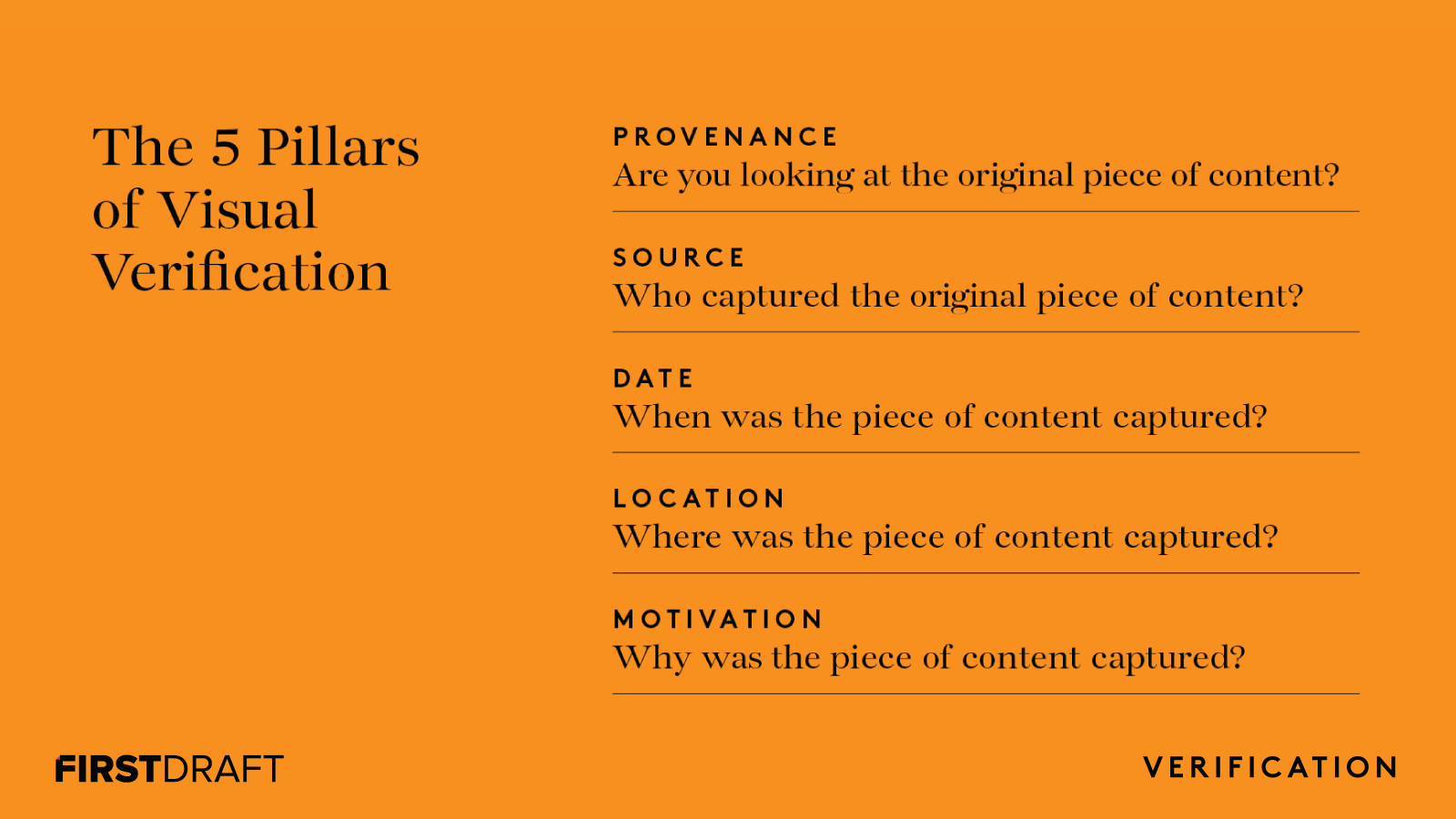
The nice thing about teaching verification is that it is easy to break down. That’s because whether you are looking at an eyewitness video, a manipulated photo, a sockpuppet account or a meme, the basic checks you have to run on them are the same:
Provenance: Are you looking at the original account, article or piece of content?
Source: Who created the account or article, or captured the original piece of content?
Date: When was it created?
Location: Where was the account established, website created or piece of content captured?
Motivation: Why was the account established, website created or the piece of content captured?
The more you know about each pillar, the stronger your verification will be.
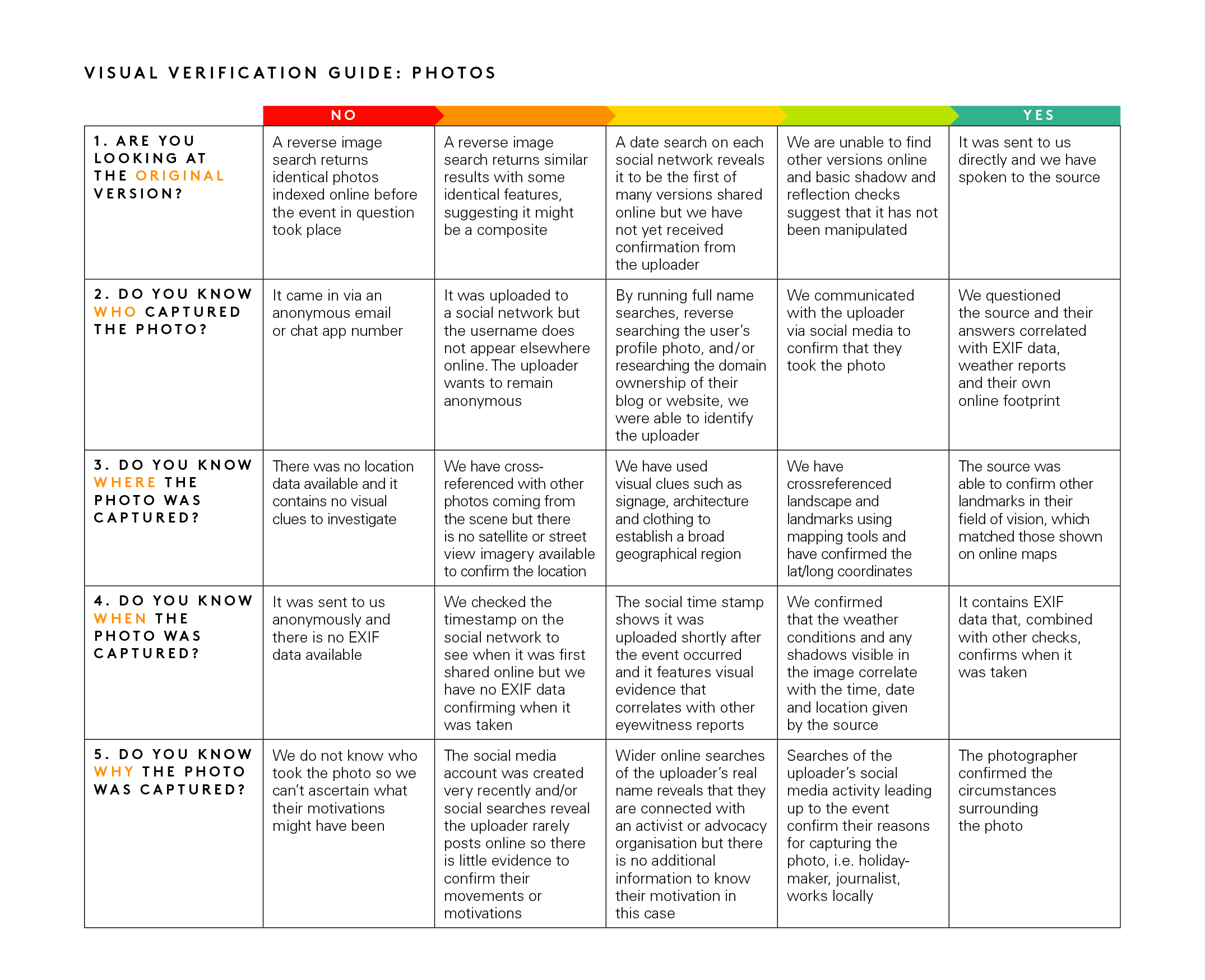
The elusiveness of certainty
Verification is hardly ever foolproof. It is more like looking for clues and collecting corroborating evidence. Picture an old-fashioned detective’s investigation board. Bits of information are pinned to the board: a location, a name, a telling quote.
Lines between the clues present a web of connections. That’s what digital verification is: the same old methods reporters and investigators have always used to get at the truth, but applied to the world wide web.
So go ahead and channel your inner Sherlock Holmes, collect as much evidence as you can, but realise that you will not always get a definitive answer. Realise also that the fact that certainty eludes us means it is all the more important we are forthright about what we know and what we don’t know — especially if that information is going to inform our reporting.
Below is a rubric we built for verifying visual media that will help you gauge how airtight your verification is, and where the holes might be.
Is this worth verifying?
Beware the rabbit hole
Often verification takes minutes. Other times it can lead you down a fruitless path of obsession. Learn to figure out when it makes more sense to give up. Also, be aware that developing too much of an attachment to one hypothesis about where a piece of content came from or whether it is true can not only compromise the integrity of your verification, it can be a big time suck.
We are human and it is easy to have a natural gut reaction to whether a piece of content is true or false. But we have to remain skeptical at all times. Remember the old editor’s adage: even if your mom says she loves you, check it out.
The internet is an expansive and cavernous place. If you are looking too intently for a particular piece of evidence, you may miss conflicting evidence along the way.
Understanding spread
Reporting on misinformation is a tricky art. Research shows that even writing ‘debunks’ can, in some circumstances, solidify false rumours in people’s minds. This means that reporting on misinformation, even when well-intentioned, can bring greater exposure to content that might have otherwise faded away.
If you are verifying a piece of misleading content because you want to report on it or write a debunk, consider first what the reach of that content is online.
How many people have seen a false claim already? It is often difficult to quantify with the metrics available, which are usually just shares, likes, retweets, views or comments. But it is important to try. Even small or niche communities can appear more significant online.
If you are looking at a piece of content which has received very low engagement, consider perhaps that it is not worth verifying or writing about.
For more information on this, read First Draft’s Essential Guide to Responsible Reporting in an Age of Information Disorder.
Tips for saving time and frustration
Screenshot everything! Content can quickly be deleted or taken down by the host platform. You might be surprised how fast you can lose crucial pieces of information. It is also important for the transparency of your verification.
- You can screenshot on Mac OS by pressing command+shift+5 and then dragging the cursor over the area you want to capture, or by using the snipping tool on Windows.
- It might be helpful to use a screen-grabbing tool like Evernote that allows you to quickly gather bits of evidence.
- Wayback Machine is a browser extension that allows you to save archived versions of webpages.
- Hunch.ly is a very powerful tool that allows you to document an entire investigation by automatically pulling in screenshots of your web browser and cataloguing them. It’s a paid tool, so not for everyone, but if you need a reliable system for documenting investigations it might be worth it.
Don’t forget to search
There are a lot of impressive tools out there for verification, and we talk about many of them in this guide. But remember that sometimes a simple Google search will do the trick.
Don’t forget to pick up the phone
In many situations, the best-case scenario is that you find a phone number or email address for a source so that you can contact them directly and ask about the content they shared. Even sending a simple direct message can start a conversation in private, where you can find out so much more than you otherwise would.
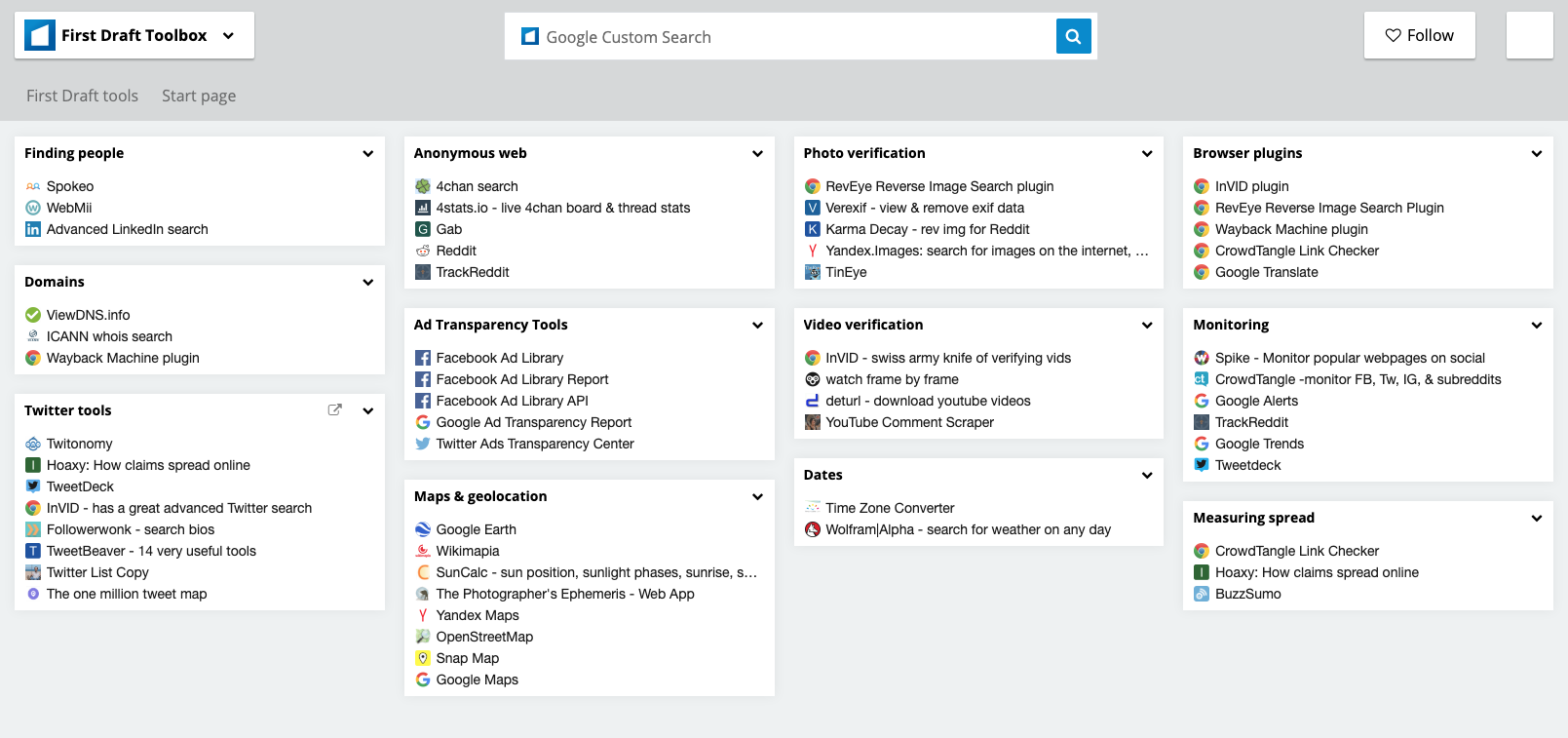
Set up a toolbox
If you are going to be doing a lot of verification or other kinds of digital research, it is worth setting up a bookmarking system that lays out all of your favourite sites. As mentioned previously, one of the biggest challenges can just be remembering the tools at your disposal.
Bookmark folders in a web browser are good, but our favourite way of saving verification tools is with a Start.me page. It displays all of your bookmarks nicely and is very fast to set up and continuously add new resources. You can use it as your home page or bookmark it somewhere else.
Monitor for related content simultaneously
While you are verifying a piece of content it can be helpful to have a monitoring dashboard and alerts system set up so that you see similar content if it surfaces. You can use keywords and language from the content you are examining to set up a search column in Tweetdeck, for example, or set up a list of accounts that often engage with your source.
Stay updated
Verification is constantly changing. Tech platforms modify their privacy settings, research tools get taken down and new ones are built. If you want to keep up, you should regularly update your toolbox or read up on the latest techniques from the verification and open source intelligence (OSINT) community. There are many public OSINT/verification lists on Twitter that you can follow to do this.
Staying safe
There are many safety precautions you should take when diving into digital investigations, but especially if you will be spending time in more closed and anonymous spaces, like Discord. Here are some basics to consider:
- Make sure you have high levels of personal digital security. Use a password a manager whenever possible.
- Examine your own digital footprint and the privacy settings on all your social accounts. How much could someone find out about you, your family and friends via your accounts?
- Consider using a VPN and an anonymous web browser like Tor.
- If you participate or interact with people in closed and anonymous spaces, be careful about the amount of personal information you divulge
Ethics and standards still apply
Digital reporting doesn’t mean basic journalistic ethics and standards go out the window. If anything, there may be new ethical considerations you hadn’t thought about. Here are a few points and questions to dwell on:
- Just as an email is not as good as an interview you did in person, neither is a quote from a post on the internet. Speak to people directly when you can.
- Some verification tools take advantage of the way social media platforms obscure privacy settings and lead people to share things they didn’t realise were public. Avoid needlessly prying into anyone’s private life.
- If you are screenshotting and documenting data from social media, understand that real people
are implicated in that data. If your systems are not secure and that data falls into other hands, you can inadvertently put people at risk. - If you are going to post anything in closed or anonymous spaces during your verification, are you going to use your real name?
- Also, are you going to be forthright in your purposes for being in those spaces?
For more on ethics and responsible reporting, see First Draft’s Essential Guide to Responsible Reporting in an Age of Information Disorder.
These are the need-to-know concepts that could save you time and potentially embarrassment.
The rest of the book is organised into five basic checks that you should do on any piece of content you wish to verify, whether it is eyewitness media, a manipulated video or a meme.
Of these chapters, ‘Provenance’ is the most important, so pay extra attention to that one. Otherwise, feel free to flip through at your leisure, or go straight to a tip list that’s relevant for you.
Verification is a fluid process of finding new clues and corroborating evidence, and the progress you make on one check might help you with another.
Stay up to date with First Draft’s work by becoming a subscriber and following us on Facebook and Twitter.